Installing Arista vEOS in VirtualBox and GNS3
November 14, 2014 5 Comments
Something that I have been looking for, for a while, has been a nice software switch that I can use that support not just switching but VLANs as well. Yes, there is Open vSwitch, but I was looking for something more traditional, if that’s the right way to say it. I heard about Arista’s vEOS switch a while back, but back then you could only download it if you were already an Arista customer. But recently I ran across another great blog post at Radovan Brezula’s blog again that shows how to setup Arista’s vEOS and that’s when I found out that I could download vEOS to try without being an already Arista customer. I swear, this guy likes playing with virtual networking as much as I do.
So below I’ll walk through my steps for setting up vEOS in VirtualBox and then putting it into GNS3 to do some basic VLAN tests.
1. Download vEOS from https://www.arista.com/en/support/software-download . You will need to create an account.
Aboot-veos-serial-2.1.0.iso
vEOS-4.14.2F.vmdk
2. Create a base vEOS VM in VirtualBox
- General:
- Name: base-vEOS
- Type: Linux
- Version: Other Linux (64bit)
- System:
- Memory: 1024MB
- CPU: 1
- Hard Drive:
- IDE Controller
- HD: Use downloaded vmdk
- CD: Use downloaded iso
- IDE Controller
- Network:
- Enable all 4 adapters and set the ‘Adapter Type’ to ‘PCNet-FAST III’
- Audio:
- Off
- Serial Ports:
- Enable Serial Port 1
- Port Number: COM1
- Port Mode: Disconnected
3. Boot it up.
The boot is a little slow to start the first time. Just wait a minute or so. When it finishes and you have the Login: prompt and you can login with ‘admin’ with no password.
Now that we have vEOS able to boot up into VirtualBox, lets add it into GNS3 for testing,
4. Make two vEOS VMs for use in GNS3
- Make sure the base-vEOS is shutdown and remove the Aboot-veos-serial-2.1.0.iso from the CD. I had issues cloning while the CD was still attached.
- My test is going to use two switches, so I cloned(linked clone) base-vEOS two times. vEOS-1 and vEOS-2.
- Add Aboot-veos-serial-2.1.0.iso back in to each cloned VM.
5. Add to GNS3
Add both new vEOS clones to GNS3 VirtualBox list following
GNS3->Edit->Preferences->VirtualBox->VirtualBox VMs->New
6. After adding both VMs, choose the each VM one at a time in the VM list in the preferences and click on the Edit button to set the following.
- General settings:
- Start VM in headless mode
- Network:
- Adapters: 4 (Adapter0 will be used for the Management1 interface. So when you set the number of adapter you need, add one extra.)
- Start at: 0
- Type: ‘PCNet-FAST III’
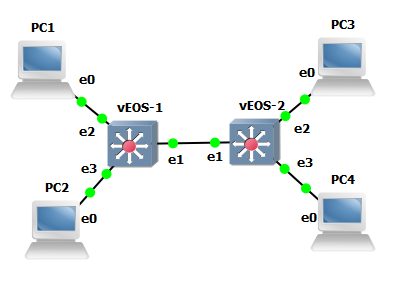
7. Add both switches to the GNS3 canvas along with four VPCS.
Create links between them
PC1 — vEOS-1 e2
PC2 — vEOS-1 e3
PC3 — vEOS-2 e2
PC4 — vEOS-2 e3
vEOS-2 e1 — vEOS-1 e1
8. Startup and configure
Now start up all the VPCS and vEOS switches. After they start up, configure the switches to have a trunk between them and set the interfaces to the VPCS to be access. To test VLANs, I’ll put PC1 and PC3 in one VLAN and I’ll put PC2 and PC4 in another.
vEOS-1:
hostname vEOS-1 enable secret arista username admin secret arista ! vlan 10 exit vlan 20 exit ! interface Ethernet1 switchport mode trunk switchport trunk allowed vlan 10,20 no shutdown exit ! interface Ethernet2 switchport mode access switchport access vlan 10 no shutdown exit ! interface Ethernet3 switchport mode access switchport access vlan 20 no shutdown exit
vEOS-2:
hostname vEOS-2 enable secret arista username admin secret arista ! vlan 10 exit vlan 20 exit ! interface Ethernet1 switchport mode trunk switchport trunk allowed vlan 10,20 no shutdown exit ! interface Ethernet2 switchport mode access switchport access vlan 10 no shutdown exit ! interface Ethernet3 switchport mode access switchport access vlan 20 no shutdown exit
PC1:
ip 192.168.1.2 /24
PC3:
ip 192.168.1.3 /24
PC2:
ip 192.168.2.2 /24
PC4:
ip 192.168.2.3 /24
9. Test it out
PC1 ping PC3
PC1> ping 192.168.1.3 192.168.1.3 icmp_seq=1 ttl=64 time=59.008 ms 192.168.1.3 icmp_seq=2 ttl=64 time=26.003 ms 192.168.1.3 icmp_seq=3 ttl=64 time=28.504 ms 192.168.1.3 icmp_seq=4 ttl=64 time=27.003 ms 192.168.1.3 icmp_seq=5 ttl=64 time=26.504 ms
PC2 ping PC4
PC2> ping 192.168.2.3 192.168.2.3 icmp_seq=1 ttl=64 time=26.004 ms 192.168.2.3 icmp_seq=2 ttl=64 time=26.503 ms 192.168.2.3 icmp_seq=3 ttl=64 time=26.004 ms 192.168.2.3 icmp_seq=4 ttl=64 time=26.003 ms 192.168.2.3 icmp_seq=5 ttl=64 time=25.503 ms
Well, it works great and does what I need it to do for a special test I want to try out, which I hope to post within the next month.
Enjoy everyone and thanks again to Radovan Brezula.
This post ‘Installing Arista vEOS in VirtualBox and GNS3’ first appeared on https://techandtrains.com/.